ADDERRA is a prepaid submetering solution for electricity and water for hotels, rental property and building owners. With the help of smart meters, smartphone application and online marketplace consumers will always pay only for what they use and owners/landlords will never remain with utility bills unpaid
Consumption management: control and limitation of water supply, prevention of water overuse, leakage and burst

Hybrid PRIME & G3-PLC benchmarking KPI 99+%
20+ years of experience

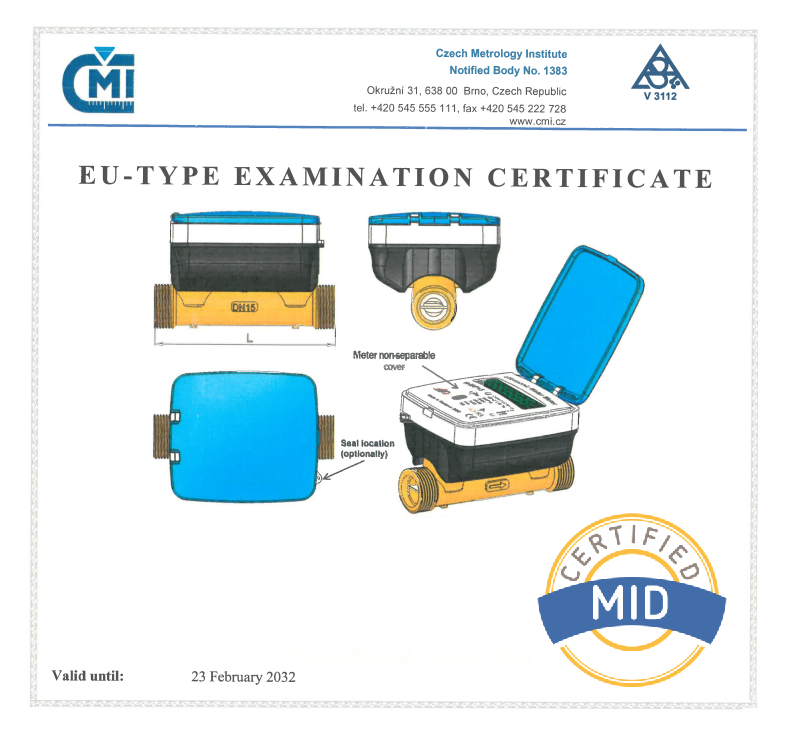
Ultrasonic Water Meter with shut off valve
A true AMI solution for measurement and control of water flow

Combining all the advantages of PLC and RF technologies into one system makes the hybrid solution from ADD GRUP the optimal choice for many purposes. Such a system can help improve the performance, reliability, capacity and scalability of the network, which leads to additional savings during system exploitation.
ADDERRA is a prepaid submetering solution for electricity and water for hotels, rental property and building owners. With the help of smart meters, smartphone application and online marketplace consumers will always pay only for what they use and owners/landlords will never remain with utility bills unpaid